Required for core functionality such as security, network management, and accessibility. These cannot be disabled.
Application Programming Interfaces (APIs) are fundamental to modern software architecture, serving as intermediaries that allow different applications to communicate and exchange data efficiently. They enable the integration of diverse systems, facilitating seamless interactions between software components. APIs are not just technical tools; they are strategic assets that can drive business growth by enabling new services and providing access to third-party services.
In the realm of API development, two prominent types are REST and SOAP. REST APIs, known for their simplicity and flexibility, use standard HTTP methods and are favored for web services due to their scalability and ease of use across various platforms. SOAP APIs, on the other hand, provide a more structured approach with strict specifications, making them suitable for scenarios that require high levels of security and transactions that need comprehensive standards compliance.
We’re going to take a closer look at the significance of APIs in the digital ecosystem, highlighting their role in enhancing connectivity, streamlining processes, and fostering innovation across industries. By understanding the fundamental aspects of API development, businesses and developers can leverage these tools to create robust, scalable, and secure applications that meet the evolving demands of the tech landscape.
Categories of APIs
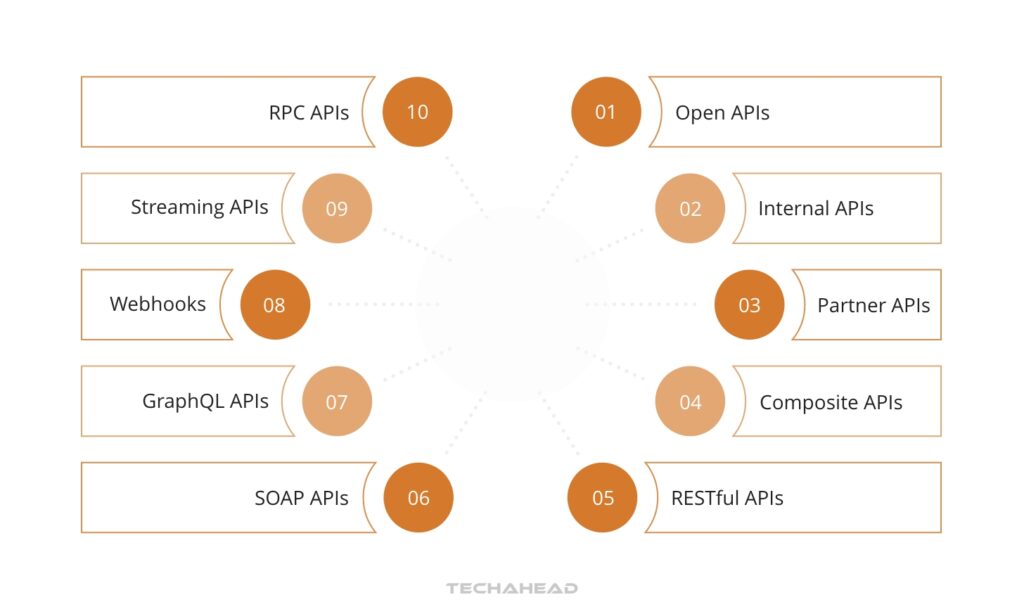
APIs can be categorized based on their accessibility and intended user base. Open APIs, also known as Public APIs, are accessible to developers and other users without restriction, fostering external innovation and the development of new services. Partner APIs are more exclusive, requiring specific rights or subscriptions for access, and are typically used in business-to-business interactions where controlled access and security are paramount.
Internal APIs or Private APIs are utilized within an organization, enhancing internal software and systems’ productivity and efficiency. They facilitate smooth communication between different departments, streamlining processes and integration within the company’s infrastructure.
Composite APIs amalgamate multiple data or service APIs to perform synchronized tasks or transactions. They are efficient in processing multiple requests, reducing server load, and are suitable for complex business processes, particularly in microservices architectures where rapid and efficient interaction between services is necessary.
Understanding these categories helps in strategically designing and implementing APIs that align with business objectives and operational needs, ensuring effective integration of services and data across platforms. This strategic approach optimizes functionality and enhances the digital solutions’ overall architecture, catering to open collaboration, secure business partnerships, and robust, multi-functional systems.
REST vs. SOAP APIs
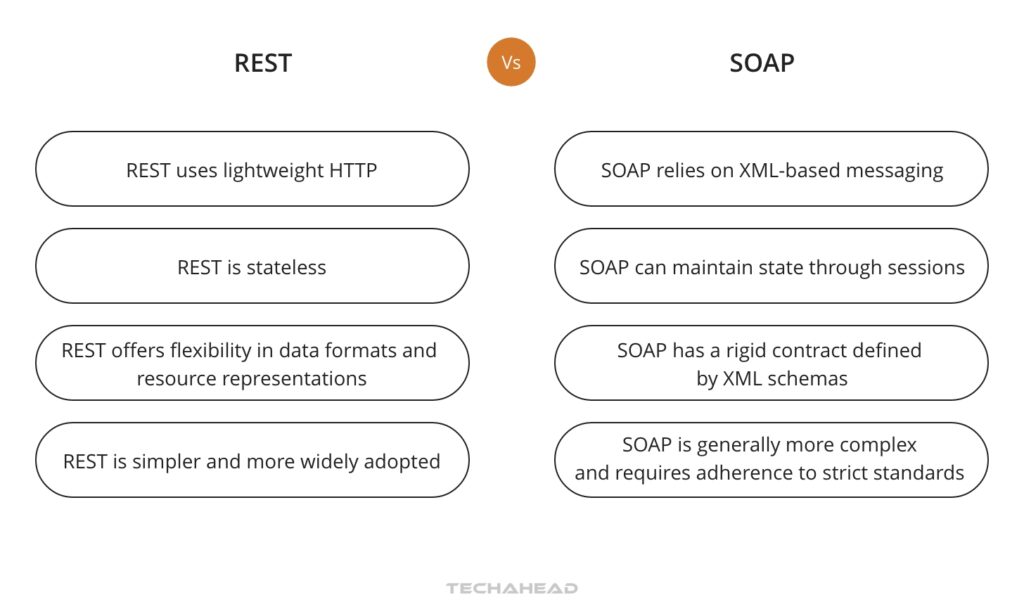
REST (Representational State Transfer) and SOAP (Simple Object Access Protocol) are two primary protocols used in API development, each with distinct characteristics and use cases. REST APIs are known for their simplicity and flexibility, utilizing standard HTTP methods like GET, POST, PUT, and DELETE. Each one is stateless, which means every request from client to server must contain everything needed to understand and complete the request, making them highly scalable and suitable for web services.
SOAP APIs, in contrast, are more structured and follow a strict set of rules, using XML for messaging. This protocol is designed for complex operations and high security, such as financial transactions and enterprise-level communications. SOAP can handle more extensive and detailed operations due to its protocol-specific service descriptions, which define the exact nature of each interaction.
The choice between REST and SOAP often depends on the specific requirements of the application. REST is generally preferred for web-based services due to its lightweight nature, ease of integration, and better performance over the web. SOAP, while more verbose and heavier on resources, provides a higher level of security and reliability, making it suitable for mission-critical applications where detailed transactions and robust security are necessary.
REST’s architecture is also conducive to internet-scale applications, supporting caching and allowing services to be easily accessible from various client types, including browsers and mobile devices. Meanwhile, SOAP’s built-in standards like WS-Reliability and WS-Security ensure reliable message delivery and secure end-to-end communications, essential in enterprise and financial applications where data integrity and security are paramount.
These protocols cater to different needs and scenarios in the API ecosystem, with REST being more suited for web-based services and public APIs, and SOAP favored in environments that require comprehensive standards compliance and transactional reliability. Understanding the operational context and requirements is key to choosing the right protocol for an API’s implementation.
Developers must consider the advantages and limitations of each to determine the most appropriate approach for their project, balancing factors like scalability, security, and the complexity of the data and operations involved.
Key API Terminology
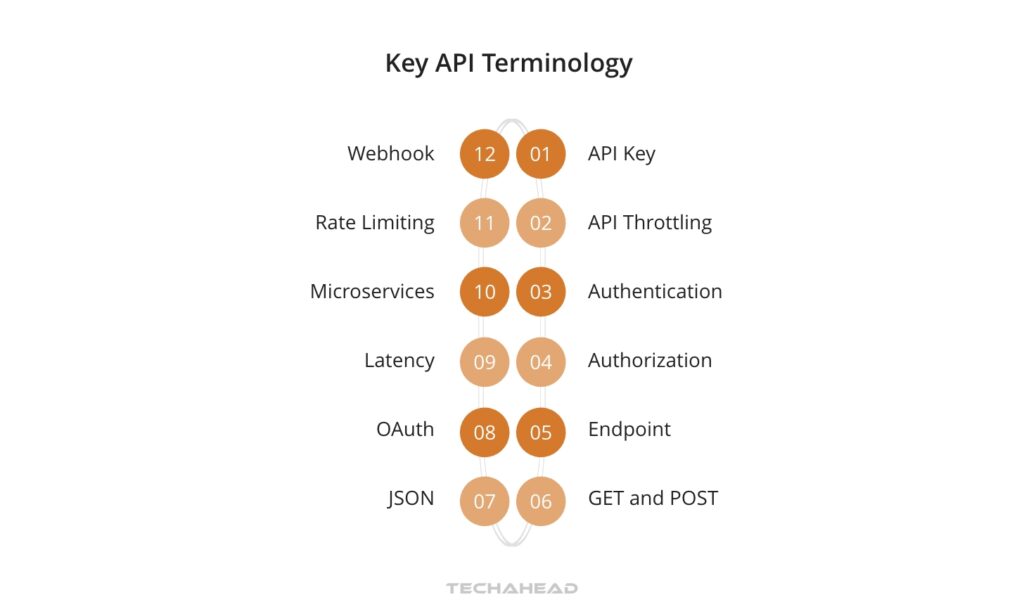
In API development, understanding the terminology is crucial for effective communication and implementation. Here are some key terms:
- API Key: A unique identifier used to authenticate a user, developer, or calling program to an API.
- API Throttling: Controls the number of API requests a user can make in a certain timeframe to prevent service overload.
- Authentication: Verifying the identity of a user or application before granting access to the API.
- Authorization: Determining what an authenticated user or application is allowed to do.
- Endpoint: The URL where an API can be accessed by a client application.
- JSON (JavaScript Object Notation): A lightweight format for data exchange, favored for its readability and ease of use in APIs.
- GET: An HTTP method used for retrieving data from a server.
- POST: An HTTP method used to send data to a server to create or update a resource.
- OAuth: An open standard for access delegation, used as a way to grant websites or applications limited access to a user’s information without exposing passwords.
- Latency: The time taken for a request to travel from the client to the server and back.
- Microservices: Microservice is a design approach to build a single application as a suite of small services, each creates a unique process and communicates with lightweight functions, such as an HTTP API.
- Rate Limiting: A technique used to control the amount of incoming and outgoing traffic to or from a network.
- Webhook: A method for augmenting or altering the behavior of a web page or web application with custom callbacks.
These terms are going to be crucial for anyone thinking about getting into API development. They help define and create an understanding of API development’s complex landscape.
Tools for API Development

In the realm of API development, a suite of tools is essential for designing, testing, and managing APIs effectively. Tools like Apigee provide a robust platform for API management, enabling developers to design, secure, and scale APIs. Dredd is an HTTP API testing framework that validates an API’s behavior against its documentation, ensuring consistency and reliability.
For specification conversion, tools like API Spec Converter play a critical role in transitioning between formats like Swagger and OpenAPI, facilitating compatibility and ease of use. APIMatic enhances developer experience by generating SDKs and documentation, streamlining the development process.
Sandbox environments are pivotal for testing, allowing developers to simulate API behavior and interactions without affecting live environments. Postman stands out as an interactive tool for running, testing, and documenting APIs, offering a comprehensive suite for API interaction. Similarly, SoapUI is renowned for its ability to automate functional and non-functional testing, ensuring APIs meet the required standards for performance and security.
Swagger, now part of the OpenAPI Specification, is instrumental in designing and documenting APIs, providing a clear and interactive interface for developers. On the performance testing front, JMeter offers capabilities to test load and stress on APIs, identifying potential bottlenecks and performance issues.
These tools collectively form the backbone of API development, offering capabilities that range from design and documentation to testing and management. They ensure that APIs are robust, secure, and capable of handling the demands of modern software applications, providing the necessary infrastructure to support the lifecycle of API development and deployment.
Core Features in API Design

Designing an effective API involves several key features that enhance functionality, usability, and performance.
- Authentication and Authorization are the pillars of security in API design, ensuring that users and systems have the correct permissions to access and interact with the API. Methods like JWT (JSON Web Tokens), OAuth, and OAuth2 are common, providing secure and efficient ways to manage user access and control.
- Query, Filter, Sorting, and Pagination mechanisms are essential for managing large datasets, allowing users to efficiently access and interact with the API’s data. These features improve the user experience by enabling precise data retrieval, reducing server load, and optimizing response times.
- Caching is another critical feature, where frequently accessed data is stored temporarily to speed up data retrieval, reducing latency, and enhancing the overall performance of the API. Tools like Memcached and Redis are often used to implement effective caching strategies.
- API wrappers are beneficial in simplifying the interaction with the API by providing a more intuitive interface for developers. These wrappers can abstract the underlying API calls into simpler, method-based interfaces, making it easier for developers to integrate and work with the API.
- HATEOAS (Hypermedia as the Engine of Application State) adds a level of discoverability to APIs, allowing clients to navigate the API through hypermedia links dynamically returned with the responses. This feature promotes a more interactive and exploratory experience for users, making the API more intuitive and easier to use.
- Error handling in API design is about providing clear, informative, and actionable feedback to clients. Well-designed APIs will have comprehensive error handling that helps developers diagnose and fix issues quickly. Standard HTTP status codes, along with detailed error messages, can significantly improve the debugging process and user experience.
- Finally, validation ensures that the data being exchanged meets the API’s expected formats and standards. Both client-side and server-side validations are important for maintaining data integrity and preventing errors during data exchange.
Incorporating these features into API design not only facilitates robust and secure interactions but also enhances the overall usability and efficiency of the API. As APIs continue to evolve, these core features will remain fundamental in building reliable, scalable, and user-friendly interfaces.
Best Practices for Designing APIs

Designing a great API involves a set of best practices that ensure its success and usability. Let’s take a look at some of those here, and point out why they’re important to be included.
Documentation
Good API documentation is essential for enabling developers to understand and use the API effectively. It should be comprehensive, detailing every aspect of the API, including endpoints, methods, possible requests, and responses. Clear examples of common use cases enhance understanding, while consistent updates ensure that the documentation reflects the latest API version
Consistency
Consistency in API design fosters a predictable and intuitive environment for developers. It involves maintaining uniform naming conventions, response formats, and behavior across all endpoints. This consistency allows developers to apply their knowledge and experience across different parts of the API, reducing learning time and decreasing the likelihood of integration errors.
Flexibility
Flexibility in API design is about anticipating future changes and enabling the API to adapt without breaking existing functionality. This approach involves designing APIs in a modular way, allowing for enhancements, updates, and new features to be added over time. Ensuring that the API can handle these changes gracefully is key to maintaining long-term usability and client satisfaction.
Security
Security in API design is non-negotiable and encompasses implementing robust authentication, encryption, and access control mechanisms. An API must protect sensitive data from unauthorized access and ensure that interactions are secure. This includes using up-to-date security protocols and regularly reviewing and updating security practices to address emerging threats and vulnerabilities.
Ease of Adoption
Ease of adoption for APIs means creating a straightforward and accessible interface that developers can quickly integrate into their projects. This includes having clear documentation, consistent and intuitive design, and reliable and responsive support. Ensuring the API can be easily tested and integrated into existing workflows significantly enhances its attractiveness and utility to developers.
Ultimately, crafting a great API is going to require a delicate balance of all these aspects. Sticking to these best practices will help create APIs that are powerful, easy to implement, and secure.
Common Security Concerns and Solutions in API Development
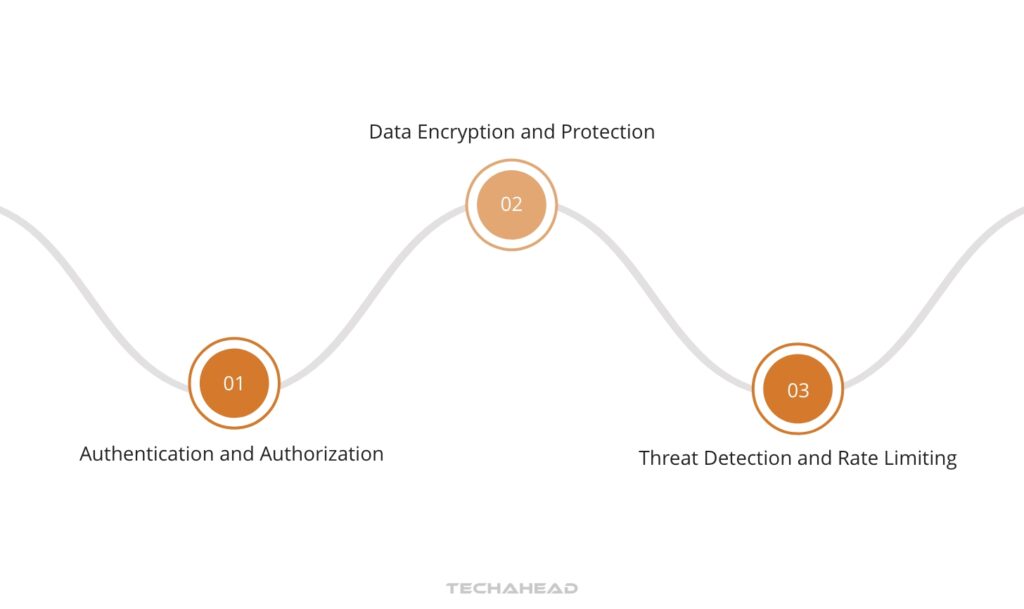
Security in API development is a critical area that addresses vulnerabilities and safeguards against attacks. It involves implementing robust authentication and authorization mechanisms, encrypting data, and employing best practices to protect the API and its users from potential threats.
Authentication and Authorization
Authentication and authorization are foundational to API security, ensuring that only legitimate users can access the API. Implementing strong, token-based authentication methods like OAuth 2.0 and JWT helps in verifying user identities and managing access permissions effectively.
Data Encryption and Protection
Encrypting data in transit and at rest prevents unauthorized access and data breaches. Utilizing TLS for secure data transmission and applying encryption standards to stored data are crucial measures for protecting sensitive information handled by APIs.
Threat Detection and Rate Limiting
Monitoring API traffic and implementing rate limiting is vital for detecting and mitigating malicious activities. Tools and practices that analyze usage patterns can help identify potential threats, while rate limiting prevents abuse by restricting the number of requests a user can make in a given timeframe.
The Future of API Development
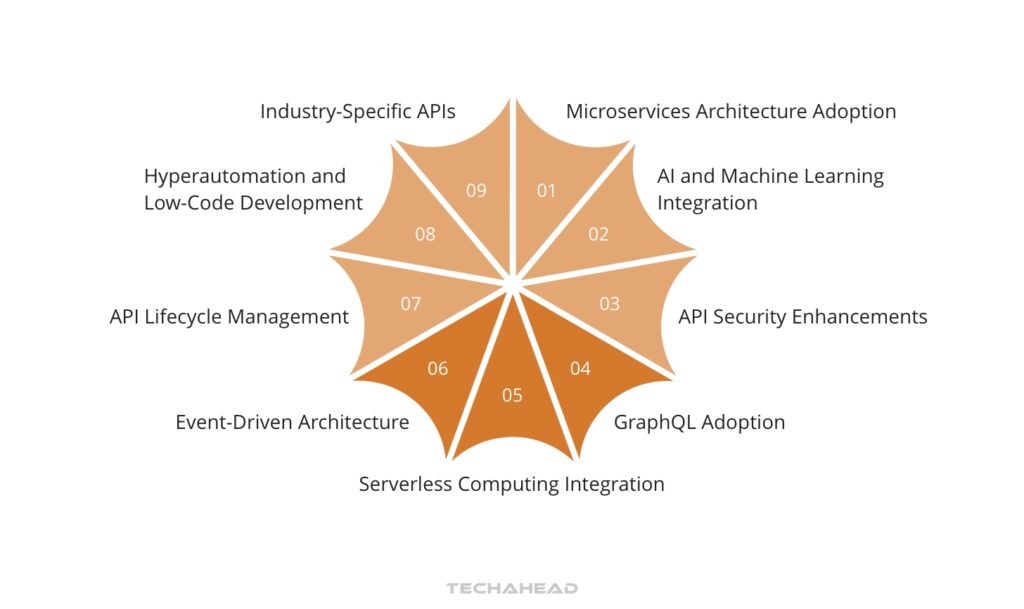
The future of API development is shaped by advancements in security, serverless architectures, AI/ML integration, and GraphQL adoption.
Enhanced security measures, including zero-trust models and advanced encryption standards, are becoming essential due to increasing cyber threats. Serverless APIs are gaining traction for their scalability and cost-effectiveness, enabling developers to focus on code rather than infrastructure.
AI and machine learning are rapidly being integrated into APIs to automate processes, provide analytics, and enhance user experiences. GraphQL is becoming a preferred alternative to REST for its efficiency in data fetching and flexibility in client queries.
Final Thoughts
API development is at the heart of modern software architecture, enabling seamless integration and communication between diverse systems. As we’ve explored, understanding API types, protocols like REST and SOAP, essential terminology, and the tools available for API development is crucial. Adopting best practices in design, focusing on security, and staying abreast of future trends are major keys to developing robust, scalable, and secure APIs.
The future of API development looks promising, with advancements in security, serverless computing, AI integration, and new query languages like GraphQL. By embracing these trends and focusing on creating user-centric, flexible, and secure APIs, developers and businesses can ensure they remain competitive and innovative in the evolving digital landscape.




