Required for core functionality such as security, network management, and accessibility. These cannot be disabled.
The cloud computing revolution has changed how we store, access, and manage information. However, this ease comes at a hefty security cost.
According to Deloitte, 69% of businesses believe AI is essential for cyber security due to the growing threats that cyber security analytics can address.
Traditional, one-size-fits-all security systems struggle to keep up with the frequently shifting threat landscape and the diverse needs of cloud users.
This is where artificial intelligence (AI) comes in, providing a valuable tool for developing individualized cloud security policies. AI can analyze massive volumes of data, identify user behavior patterns, and predict possible risks with unprecedented accuracy.
Organizations can improve their cloud security posture by harnessing AI’s analytical capacity and machine learning capabilities. The article discusses the exciting prospects of AI-powered cloud security, including the benefits of personalized approaches and practical ideas and strategies for implementation.
Fast Facts and Statistics
- According to Thalesgroup, over half (55%) of IT and security experts cited human error as the main reason behind cloud data breaches.
- Security practitioners at Cloud Security Alliance reported the most prevalent security issues as loss of sensitive data (64%), poor setup and privacy settings (51%), and unauthorized access (51%), when deploying apps in the public cloud.
- According to the AI Index report, the total spending on artificial intelligence in the cloud industry amounted to around $5.9 billion in 2022.
- According to Statista, the global market for public cloud computing is predicted to expand further and reach an estimated 679 billion dollars by 2024.
- Another Statista survey says that the global revenue in the cloud security market was expected to constantly expand between 2023 and 2028 by a total of 6.7 billion USD.
Key Takeaways
- AI customizes security measures based on individual user profiles and data sensitivity, providing a more efficient and effective solution than traditional one-size-fits-all approaches.
- AI excels in analyzing large volumes of cloud data, allowing real-time threat detection, anomaly identification, and even proactive security measures to predict and avoid assaults.
- AI automates early security responses, aids in incident investigation, and can even launch self-healing measures in a cloud environment to reduce downtime and human error during security breaches.
How Does AI Help with Personalized Cloud Security?
AI personalizes cloud security by adapting protection to specific users and data requirements. Here’s how.
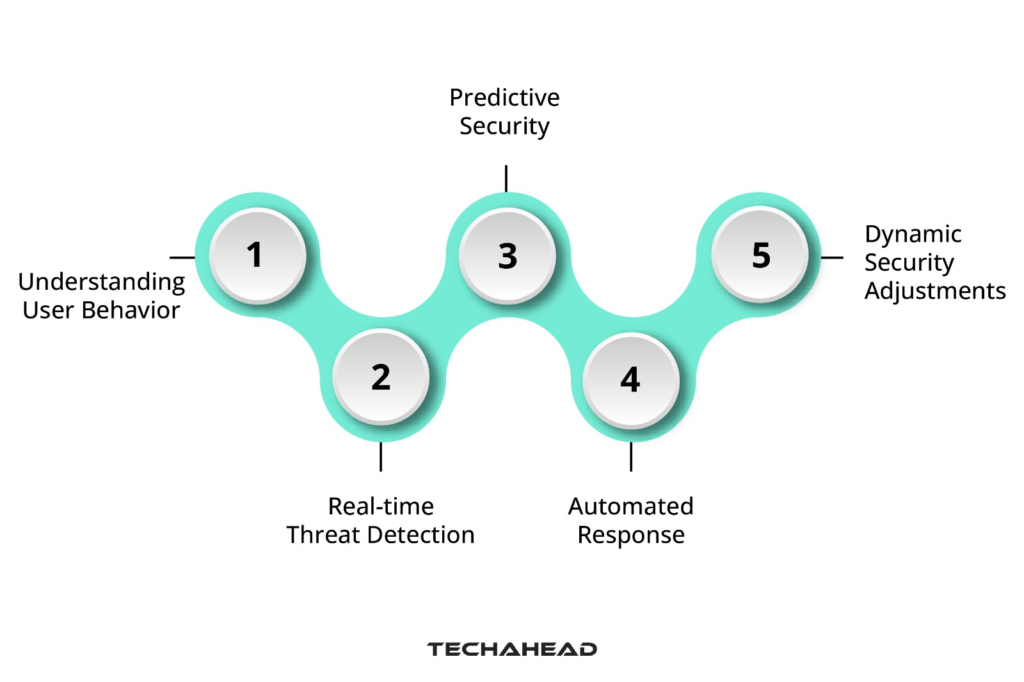
Understanding User Behavior
Artificial intelligence examines user activity, data kinds, and access patterns. This enables it to generate a unique security profile for each user, recognizing high-risk actions or sensitive data that require further protection. Consider how a financial organization must make tougher efforts to protect customer data than someone who stores personal images.
Real-time Threat Detection
Unlike traditional approaches, AI can evaluate massive cloud data volumes in real-time. This allows it to detect suspicious actions and anomalies that may differ from established user baselines. Early identification enables faster intervention and stops potential breaches.
Predictive Security
AI uses previous data and threat intelligence to predict potential threats. This enables proactive security steps, such as banning suspect IP addresses or deploying additional security protocols before an attack occurs.
Automated Response
When risks are discovered, AI can automatically initiate predefined security responses. This streamlines incident response lowers human error, and narrows the window of opportunity for attackers.
Dynamic Security Adjustments
AI models can constantly learn and adapt. This allows them to quickly alter security policies in response to new threats and user behavior. Consider AI automatically strengthening security measures when a user exhibits anomalous access behaviors.
Tips to Develop and Implement An AI-Powered Cloud Security System
You must take a holistic and secure approach to integrate AI into your cloud security strategy successfully. Here’s a step-by-step guide on handling this process.
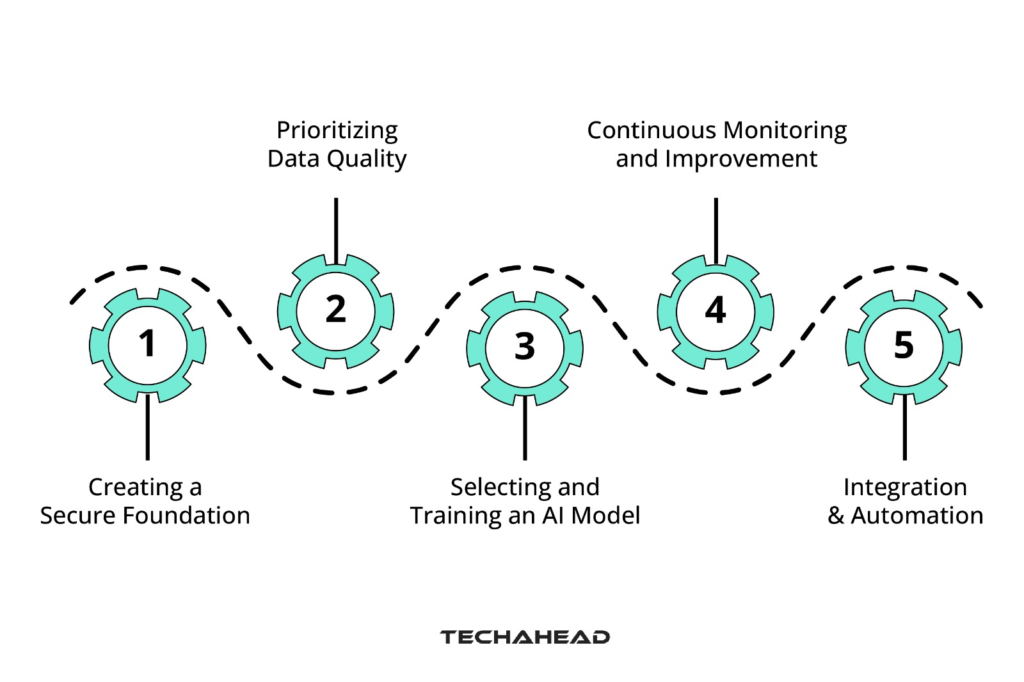
1. Creating a Secure Foundation
The foundation of every AI system is strong security. Before implementation, ensure that your cloud infrastructure follows the industry’s best data security and access management practices. This reduces the likelihood of bad actors manipulating the AI system, jeopardizing your overall security posture.
2. Prioritizing Data Quality
The quality and relevance of the training data determine the effectiveness of AI models. Focus on collecting high-fidelity, labeled data that appropriately reflects your cloud environment and security requirements.
3. Selecting and Training an AI Model
Consult with AI development agency to choose an AI model architecture compatible with your specific cloud security needs. Consider scalability, explainability (the ability to comprehend the reasoning behind the model’s decisions), and resource requirements.
4. Integration & Automation
Seamlessly integrating your AI model with your existing security infrastructure is critical. This allows the model to automatically generate security warnings, enforce security regulations in real-time, and start predetermined responses to identified risks.
5. Continuous Monitoring and Improvement
The cybersecurity threat landscape is continuously changing. As a result, it’s critical to routinely check your AI system’s performance, assessing its effectiveness in detecting risks and avoiding breaches. To retain accuracy and respond to changing difficulties, update your AI model regularly with new data and threat information.
Using AI for Personalized Security Measures
Major cloud providers are driving the charge for personalized security by leveraging AI. These AI-powered technologies assess your cloud environment and data to personalize protection measures, resulting in a more efficient and effective defense.
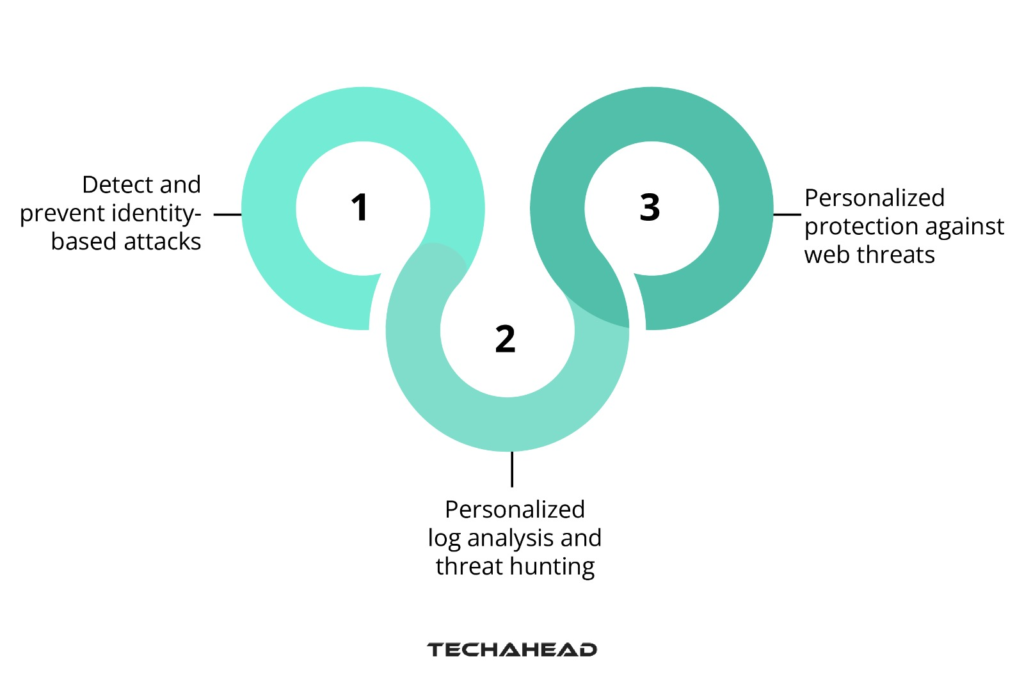
Below are a few examples of how AI personalizes cloud security across key cloud platforms:
- Azure AD Identity Protection: This cloud-based security service uses artificial intelligence and machine learning to detect and prevent identity-based attacks such as phishing and password spraying. By studying user behavior patterns and login attempts, it can detect suspicious activity and prevent illegal access to your cloud assets.
- Chronicle: Google’s cloud-based SIEM product uses AI for log analysis and threat hunting. It enables you to design bespoke threat detection criteria based on your unique security requirements and data sources, resulting in personalized threat information beyond generic warnings.
- Cloud Armor: This web application firewall (WAF) service uses machine learning to detect and prevent harmful attacks on GCP-deployed web applications and APIs. Cloud Armor personalizes its defense against evolving web threats based on attack patterns and traffic behavior.
AI’s Role in Cloud Computing Future
The cloud market’s revenue growth may stall as cloud computing spreads throughout industries. However, as large IT businesses increasingly utilize AI capabilities in the cloud, the AI boom is predicted to revitalize cloud computing. One project that focuses on generative AI on the cloud is Amazon’s Bedrock cloud service. With AI-generated text, developers can effectively improve their applications, showcasing AI’s potential in cloud computing.
In the future, AI will improve efficiency in the cloud by intelligently allocating resources and finding problems. Through predictive analytics, it will also make the experiences of users more unique and lower the costs.
I have not seen this level of engagement and excitement from customers, probably since the very, very early days of cloud computing. – Dr. Matt Wood, VP of Artificial Intelligence at AWS 2023
Utilize AI for Personalized Cloud Security with TechAhead
TechAhead can assist you in developing a personalized security strategy for your cloud environment using AI. Our specialists will guide you through installing AI-powered security solutions, ensuring your data is secured from increasingly complex cyber threats. Contact TechAhead today to learn more and gain control of your cloud security posture.
Summary
AI provides an effective response by providing personalized cloud security techniques. AI enables enterprises to build proactive and dynamic defenses by analyzing massive volumes of data, finding user behavior trends, and forecasting future threats. This improves overall security and the user experience by eliminating unnecessary hurdles.
FAQ’s
Q. How can AI be used to improve cloud security?
Use AI to assess cloud data for real-time threat detection, tailor security based on user behavior, and automate actions to achieve a proactive and efficient cloud security posture.
Q. How can AI be utilized to improve security systems?
AI can analyze massive volumes of cloud data in real-time, allowing for threat detection, anomaly identification, and even prediction of possible attacks to improve security proactively.
Q. What are the five important components of an effective cloud security strategy?
A five-pronged cloud security strategy includes data encryption, effective identity and access management, continuous monitoring and incident response, security audits and compliance checks, and employee security awareness training.