Required for core functionality such as security, network management, and accessibility. These cannot be disabled.
Your enterprise is connected across 15 countries, running thousands of IoT devices, processing real-time data around the clock. Sounds like a competitive advantage, until one unpatched sensor in your Dallas warehouse quietly hands attackers access to your entire network.
That is not a hypothetical. That is the reality facing enterprises in 2026. With over 21 billion connected devices globally, IoT has become the backbone of modern enterprise operations.
However, here is the uncomfortable truth; attacks on IoT endpoints jumped 107% in a single year, and the average breach now costs enterprises up to $4.88 million. Growth without security is not ambition. It is exposure.
The good news? Scaling securely is absolutely possible.
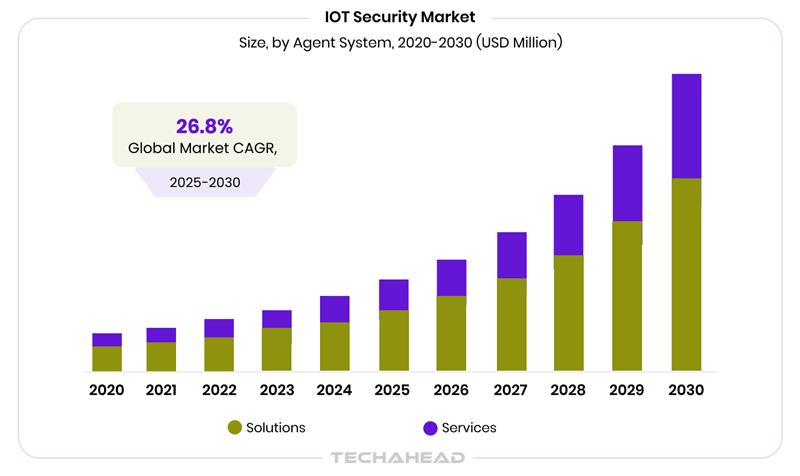
According to Grand View Research, the global IoT security market size was estimated at USD 35.50 billion in 2024 and is projected to reach USD 141.77 billion by 2030, growing at a CAGR of 26.8% from 2025 to 2030.
That is exactly what this blog is for, we are going to explore everything from zero-trust architecture and multi-region device security to global compliance frameworks, real-time threat detection; so your IoT ecosystem grows smarter.
Key Takeaways
- Treating security as infrastructure from day one prevents far costlier fixes later.
- Edge computing minimizes data in transit risks by processing information locally.
- Shadow IoT devices are among the fastest-growing and least visible enterprise risks.
- Every new market you enter multiplies your attack surface significantly.
- Zero-Trust is a mandatory baseline for global interoperability.
Why Scaling IoT Globally is a Security Nightmare (And How to Fix It)?
There are nearly 23 billion IoT devices in operation today, and that number keeps climbing. For enterprise owners, this growth is both an opportunity and a serious liability. Every new market you enter adds devices, networks or new regulatory layers, which most of the attackers know.
The risks are not theoretical. They are happening right now:
- IoT endpoint attacks jumped 124% (2025-2026), with attacks lasting over 52 hours per week on average.
- IoT security failures cost businesses an average of $330,000 per incident.
The fix starts with treating security as infrastructure. Enterprises that scale securely embed zero-trust principles from day one, enforce strict device authentication across regions before entering new markets, not after a breach forces them to.
Understanding IoT Security Threats in 2026
Billions of connected devices. Evolving attack methods. Rising breach costs. Here is what your enterprise is actually up against in 2026.
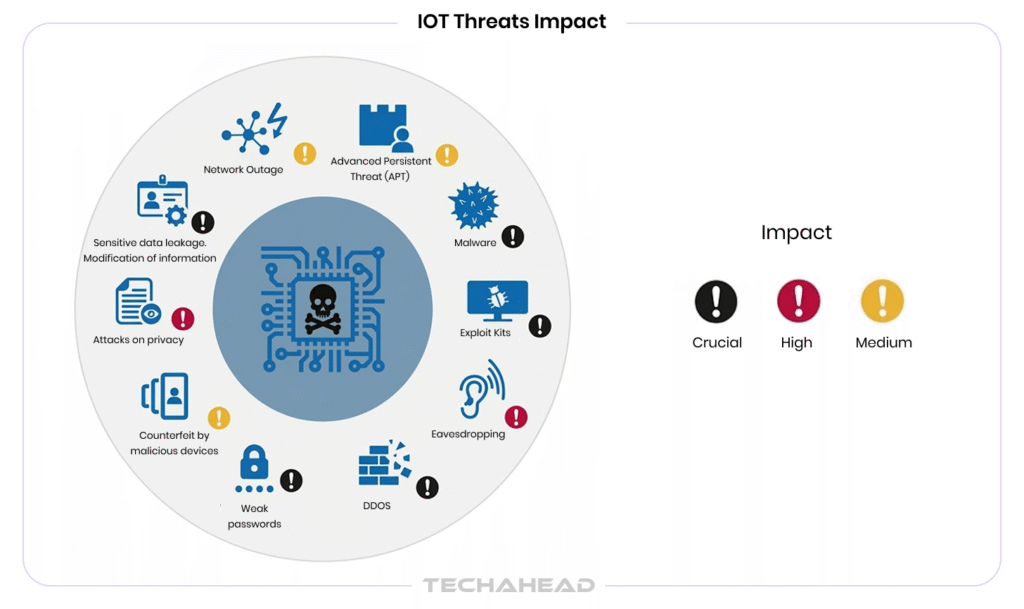
The Scale of the Problem is Already Beyond What You Think
IoT device counts are projected to surpass 23 billion in 2026. If you are running operations across multiple regions, that number is not abstract; it directly represents your attack surface. And the volume alone is not the issue. It is the speed at which attackers are moving.
What You Are Actually Up Against?
In 2025, there were over 820,000 malicious IoT attack attempts every single day, a 46% increase from the prior year. IoT malware also spiked by 124% year-over-year. However, these are not random incidents. Attackers are running automated tools that scan, identify, and exploit vulnerable endpoints faster than most enterprise security teams can respond.
The Weak Points Hiding in Plain Sight
Here is what makes your infrastructure vulnerable right now. Around 57% of IoT devices are susceptible to medium or high-severity attacks, 65% do not perform mutual authentication with the server. If your devices are still using default credentials or outdated firmware, you are essentially leaving the door open.

Why This Hits Global Enterprises Hardest
When you scale across borders, your risk multiplies. Different regions mean different network environments, compliance requirements, and device standards; all creating gaps attackers are quick to exploit. By 2026, effective threat detection must correlate signals across OT, IoT, and edge domains together for unified visibility.
Building a Zero-Trust Architecture for Your IoT Ecosystem
Zero-trust means never assuming safety. Here is how to build it into your IoT ecosystem from the ground up.
What Zero-Trust Actually Means for Your Business?
Forget the old “trust but verify” model. Zero-trust flips it entirely; never trust, always verify. Every device, user, and connection in your IoT network is treated as a potential threat until proven otherwise. No exceptions.
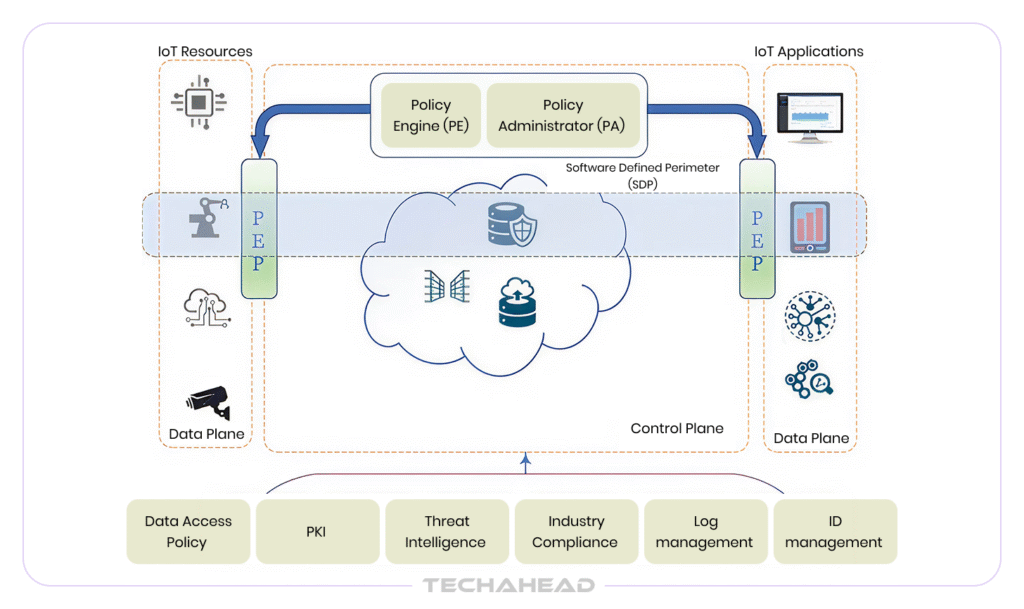
According to Forrester Research, organizations with mature zero-trust implementations experience 50% fewer breaches and reduce breach costs by an average of 43%. In short, it is not a small margin, it is a business advantage.
The Three Pillars You Cannot Skip
Your zero-trust strategy is only as strong as these pillars. Without these three, your zero-trust architecture is incomplete and vulnerable.
Verify Every Device Identity
Your IoT ecosystem is only as secure as its weakest endpoint. Before any device communicates across your network, it needs a verified identity.
- Assign unique digital certificates to every device
- Enforce mutual authentication; the device verifies the server, and the server verifies the device
- Eliminate default credentials entirely
Apply Least-Privilege Access
Not every device needs access to everything. So,
- Segment your IoT devices from core business systems
- Grant access on a per-session basis, not permanently
- Use micro-segmentation to contain lateral movement if a breach occurs
Monitor Continuously, Not Periodically
One-time checks do not work. In 2026, zero-trust means enforcing identity, segmentation, and policy as continuous behaviors rather than scheduled tasks. For example:
- Deploy real-time anomaly detection across all endpoints
- Log every access request, every device interaction
- Automate alerts when behavior deviates from defined baselines
72% of organizations now favor a zero-trust approach, so it is crucial if you are scaling IoT across global markets.
Global Compliance and Regulatory Requirements for IoT
Expanding your IoT ecosystem across borders is not just a technical challenge; it is a legal one. Every market you enter brings its own set of rules, and the penalties for getting it wrong are steep. Under GDPR alone, non-compliance can cost you up to €20 million or 4% of your global annual turnover. That is before you factor in reputational damage and operational disruption.
The regulatory landscape is tightening fast. Here are the key frameworks you need to have on your radar right now:
EU Cyber Resilience Act (CRA)
Vulnerability reporting obligations kick in from September 11, 2026, with full enforcement from December 11, 2027. If you sell connected products in Europe, this is non-negotiable.
GDPR & NIS2
Both apply to IoT data processing and network security across EU member states. NIS2 specifically extends obligations to supply chain security.
US Frameworks
NIST’s IoT Cybersecurity Framework and CCPA apply depending on your sector and the states you operate in.
Asia-Pacific
China’s updated Cybersecurity Law, effective January 2026, now extends to any foreign entity whose activities affect China’s network security IoT M2M Council, which is a significant shift for global operators.

Data Localization Laws
Countries like India, Russia, and Indonesia require certain data to be stored locally. Several countries now restrict or outright prohibit international data transfers without formal approval.
The biggest mistake enterprises make? Treating compliance as a checkbox after deployment. Build it into your architecture from the start. Map each market’s requirements before a single device goes live. That is the only way to scale without legal landmines waiting for you.
Securing IoT Devices Across Multi-Region Deployments
The Attack Surface Grows With Every New Region You Enter
Deploying IoT devices across multiple geographies is not the same as deploying them in a single environment. Each region introduces different network topologies, carrier infrastructure, regulatory requirements, and physical security risks.
60% of IoT devices carry unpatched known CVEs (Common Vulnerabilities and Exposures) older than two years, and when you scale that across hundreds or thousands of endpoints spread across continents, the exposure compounds fast. Visibility is the first thing you lose. Control is the second.
Device Identity and PKI are Non-Negotiable at Scale
Every device operating across your global infrastructure must carry a cryptographically verifiable identity. It means deploying a Public Key Infrastructure (PKI) that issues unique X.509 digital certificates to each endpoint.
The modern IoT security paradigm is “Zero Trust at the Edge,” where every interaction, whether a sensor talking to a gateway or a smart meter reporting to the cloud must be authenticated via Mutual TLS (mTLS).
Self-signed certificates will not cut it. You need a trusted Certificate Authority (CA) with automated Certificate Lifecycle Management (CLM) to prevent expiration failures, which in multi-region deployments can silently take entire device clusters offline.
OTA Firmware Updates Must Be Secure and Verifiable
Patching thousands of devices manually across global deployments is operationally impossible. Over-the-Air (OTA) firmware updates solve the scale problem, but only when implemented correctly.
In PKI-backed OTA systems, the manufacturer signs the update package with a private key, and the IoT device verifies it using the corresponding public key, rejecting any update that fails the signature check.
Combine this with secure boot, TLS-encrypted transmission channels, and staged rollout mechanisms to minimize the blast radius of a flawed update hitting your entire global fleet at once.
Network Segmentation Prevents Lateral Movement
A compromised device in your Singapore facility should never have a path to your core infrastructure in Frankfurt. Micro-segmentation at the network layer, moving beyond traditional VLANs to Identity-Based Access Control.
In that case, even if a sensor is breached, its ‘blast radius’ is limited to a single encrypted tunnel. Moreover, Deep Packet Inspection (DPI), correlated with DHCP, DNS, and ARP logs, helps build dynamic asset maps to detect compromised endpoints across distributed environments. Without this, one breached sensor becomes a doorway into everything.
The Role of Edge Computing in Secure IoT Scaling
In 2026, the edge isn’t just about speed; it’s about sovereignty.
Sending every byte of data from thousands of devices to a centralized cloud is not just slow; it is a security liability. Edge computing solves this by processing data locally, closer to where it is generated. Gartner predicts that 75% of enterprise data will be handled at the edge, up from just 10% in 2018. However, we have officially entered the era where the majority of enterprise data is generated and processed outside traditional centralized data centers.
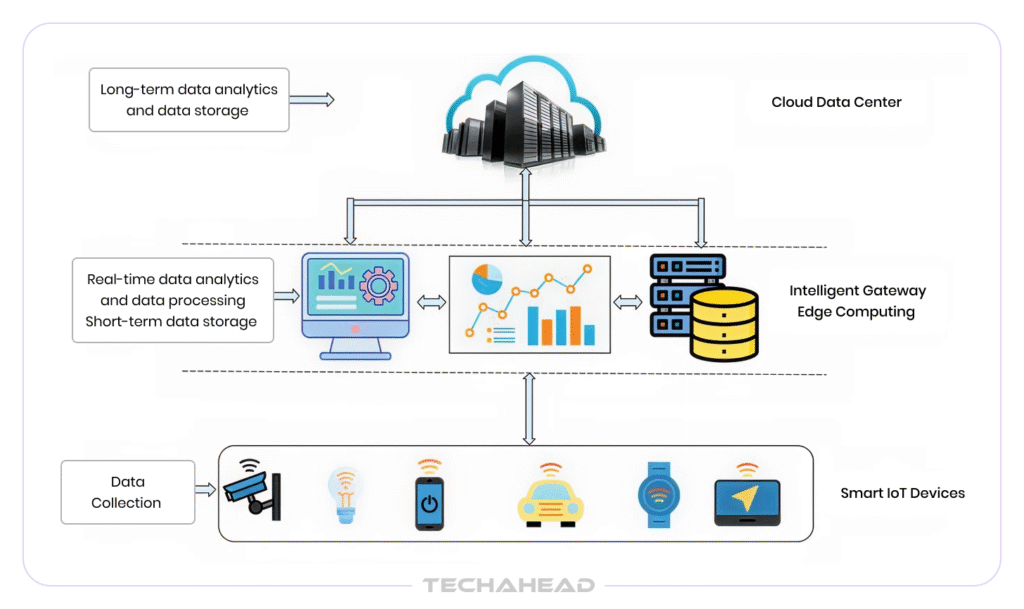
For global IoT deployments, this matters enormously. When sensitive data stays within a regional edge node rather than traveling across borders, you reduce both latency and exposure to interception. Fewer data transfers mean fewer attack windows.
Because edge infrastructure frequently sits outside traditional enterprise perimeters, identity management, secure communication protocols, automated threat detection must be built into the design from the start.
The total number of edge-enabled IoT devices is projected to reach 5.8 billion in 2026, a 13% increase from 2025. That growth is not slowing down. Enterprises that embed security into their edge architecture today will scale without dragging new vulnerabilities into every new market they enter.
Cost vs. Security: How to Balance IoT Scaling Without Compromising Protection?
Many enterprise owners treat IoT security as a cost center. That is the wrong frame entirely. The average cost of a successful breach on a single IoT device is $330,000, while enterprise IoT breaches range between $5 million and $10 million. Compare that against the cost of prevention. The numbers make the decision obvious.
The real expense is not securing your IoT ecosystem, it is recovering from not securing it. A single data breach from an unmonitored IoT device can cost more than years of preventive investment. Moreover, downtime, regulatory fines, reputational damage, and customer loss add up fast. And prevention is always cheaper.
Automation is where you find your savings. Manual certificate management, device monitoring, and patch deployment across thousands of global endpoints drain both budget and team bandwidth. Automating these processes cuts operational overhead significantly and removes the human error that causes most incidents in the first place.
Organizations implementing microsegmentation see 45% lower breach costs when incidents occur: $2.68 million versus the $4.88 million average. However, it is not a marginal saving. Targeted, high-impact investments like segmentation and zero-trust deliver measurable ROI without rebuilding your entire infrastructure.
Conclusion
Scaling your IoT ecosystem across global markets is not a question of if you will face security challenges; it is a question of how prepared you are when they arrive. From zero-trust architecture and multi-region device management to real-time threat detection and global compliance, every layer of your IoT infrastructure demands security-first thinking.
The enterprises that will win in the connected economy are not those with the most devices. They are the ones who scale smartly, build security into every deployment decision, and treat protection as a business advantage rather than an operational burden. That is exactly where TechAhead comes in.
With 16+ years of experience, ranked #1 globally on Clutch’s Top App Development Company, and holding SOC 2 Type II and ISO 27001 certifications, TechAhead builds enterprise IoT ecosystems that are scalable and secure across every market you operate in. Scale your IoT ecosystem without the security risks. Consult with TechAhead today and let us show you how.
Isolate them into strictly segmented network zones, disable all non-essential ports. You can also enforce tighter access controls, and monitor them continuously. In short, a device you cannot replace must be the one you watch most closely.
5G’s speed and scale expand your attack surface significantly, requiring network slicing controls, stronger device authentication, and security built into your architecture from day one.
Shadow IoT refers to unauthorized connected devices active within your organization without your IT team’s knowledge. You can detect them using continuous network scanning; Deep Packet Inspection, and automated asset discovery tools that flag any unregistered device the moment it connects.
Neither alone is sufficient. Most enterprises operating globally need a hybrid approach, such as cloud for centralized visibility and scalability, on-premise or edge processing for data sovereignty, low latency, and compliance with regional data localization laws.